Quantum Cryptography: The Future of Unbreakable Digital Security
The encryption protecting your data today could be broken by tomorrow’s quantum computers. Quantum Cryptography is the answer — and understanding it is no longer optional for any serious business or security professional in 2026.
Quantum Cryptography is rapidly emerging as one of the most critical fields in modern cybersecurity — and the reason is urgent. Right now, the encryption standards protecting virtually every sensitive digital transaction on the planet are built on a mathematical assumption: that certain calculations are so complex no computer could solve them in a practical timeframe. For classical computers, that assumption holds. But quantum computers, which harness the laws of quantum mechanics to process information in fundamentally different ways, threaten to shatter that assumption entirely.
The race between quantum computing power and cryptographic defense is one of the defining technology battles of our era. Quantum Cryptography sits at the heart of that battle — offering not just protection against quantum attacks, but in some forms, security guarantees rooted in the laws of physics themselves rather than mathematical complexity alone.
In this article, we break down exactly what Quantum Cryptography is, how it works, how it differs from post-quantum cryptography, where it is being deployed today, and what organizations must do right now to secure their digital future against the quantum threat.
What Is Quantum Cryptography and Why Does It Matter?
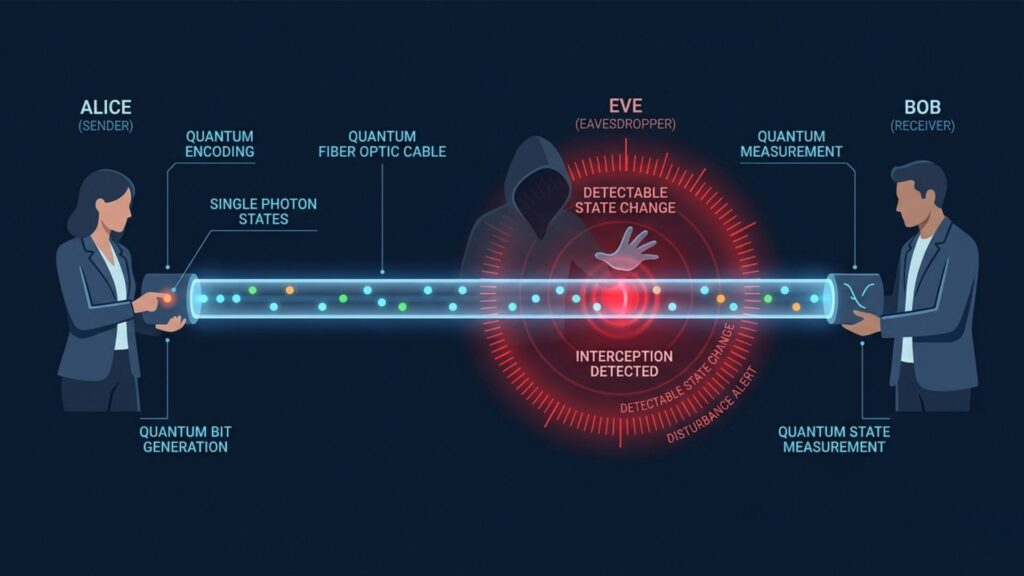
Quantum Cryptography is the science of using quantum mechanical principles to secure information in ways that are theoretically impossible to compromise without detection. Unlike classical cryptography, which relies on mathematical problems that are computationally difficult but not physically impossible to crack, Quantum Cryptography derives its security from the fundamental behavior of quantum particles.
The most well-known and practically deployed application of Quantum Cryptography is Quantum Key Distribution — commonly known as QKD. This is a method of securely exchanging encryption keys between two parties using quantum particles, typically photons of light. The security guarantee it offers is extraordinary: any attempt by an eavesdropper to intercept or measure the quantum particles used to transmit the key inevitably disturbs those particles in a detectable way. The laws of quantum mechanics make silent, undetected interception physically impossible.
Classical encryption says: this lock is too hard to pick. Quantum Cryptography says: this lock will always tell you if someone tried — because the laws of physics make silent interception impossible.
This distinction is enormously significant. In a world where quantum computers are advancing toward the capability to break mathematical encryption, having a security model grounded in the immutable laws of physics rather than computational difficulty represents a qualitative leap forward in how we think about protecting sensitive information.
The Quantum Threat That Makes Quantum Cryptography Urgent
To appreciate why Quantum Cryptography matters so urgently right now, you need to understand the specific threat quantum computing poses to existing security infrastructure.
How Current Encryption Works
Most encryption securing the internet today — including RSA and elliptic curve cryptography underpinning HTTPS, TLS, and digital certificate systems — relies on the mathematical difficulty of specific problems. RSA encryption depends on the fact that while multiplying two very large prime numbers is easy, factoring the result back into its original components is computationally prohibitive for classical computers. A 2048-bit RSA key would take a classical computer longer than the current age of the universe to crack by brute force.
Why Quantum Computers Break the Rules
In 1994, mathematician Peter Shor developed a quantum algorithm — now called Shor’s Algorithm — that can factor large numbers exponentially faster than any classical algorithm. On a sufficiently powerful quantum computer, this algorithm could break 2048-bit RSA encryption in hours rather than billions of years. Grover’s Algorithm, another quantum computing breakthrough, similarly threatens symmetric encryption by effectively halving the security strength of key lengths.
The implication is stark: when fault-tolerant quantum computers with enough stable qubits arrive — serious estimates range from five to fifteen years — most of the encryption protecting global digital communications will become vulnerable.
Harvest Now, Decrypt Later: The Threat Is Already Here
Perhaps the most urgent near-term threat does not require quantum computers to exist yet. Intelligence agencies and sophisticated adversaries are already engaged in what experts call harvest now, decrypt later attacks — collecting and storing encrypted data today with the intention of decrypting it once quantum computers become powerful enough. For any data that must remain confidential for a decade or more — classified intelligence, long-term financial records, sensitive medical histories, trade secrets — this threat is not hypothetical. It is active right now. That is the reason Quantum Cryptography has moved from academic research to boardroom urgency.
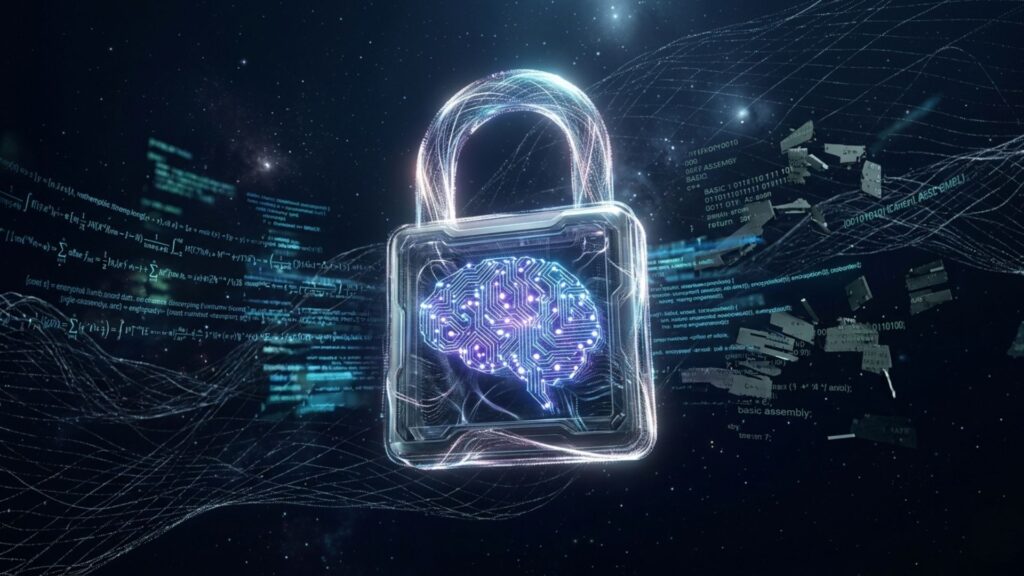
Quantum Cryptography vs Post-Quantum Cryptography: Key Differences
These two terms are frequently confused — and the distinction matters enormously when organizations are making security investment decisions.
Post-Quantum Cryptography (PQC)
Post-quantum cryptography refers to classical mathematical algorithms — ones that run on ordinary computers — that are designed to be resistant to attacks by quantum computers. They do not use quantum mechanics. Instead, they rely on mathematical problems that quantum computers are not believed to be able to solve efficiently, such as lattice-based problems, hash-based signatures, and code-based cryptography.
Post-quantum cryptography is the practical near-term solution for most organizations. The US National Institute of Standards and Technology finalized its first post-quantum cryptography standards in 2024, providing organizations with concrete, implementable replacements for current vulnerable algorithms. PQC can run on existing hardware and integrate with existing software infrastructure — which makes it far more accessible than quantum hardware solutions.
Quantum Cryptography (QKD and Beyond)
Quantum Cryptography, by contrast, uses actual quantum hardware — specialized devices that generate, transmit, and detect quantum particles — to achieve its security guarantees. It is not just resistant to quantum attacks; in the case of QKD, it provides information-theoretic security, meaning its security holds even against an adversary with unlimited computing power, including quantum computers.
The tradeoff is practical deployment complexity. Quantum Cryptography requires specialized infrastructure — quantum-enabled fiber optic networks or satellite-based quantum communication links — that is expensive, limited in range without quantum repeaters, and not yet widely available. For most organizations today, post-quantum cryptography is the right immediate priority, with Quantum Cryptography representing the gold standard for the highest-security applications.
Think of it this way: Post-quantum cryptography is a new, stronger lock designed to resist quantum lockpicks. Quantum Cryptography is a lock that physically alerts you the moment anyone touches it — regardless of what tools they use.
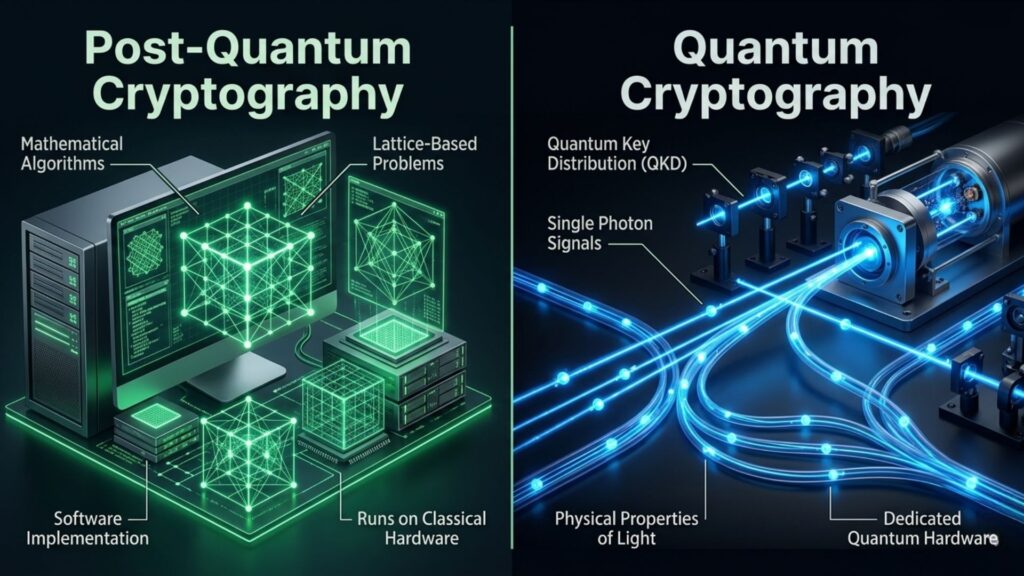
How Quantum Key Distribution Works in Practice
Quantum Key Distribution is the most mature and widely deployed form of Quantum Cryptography. Here is how it works in practical terms:
The BB84 Protocol — The Foundation of QKD
The most widely used QKD protocol, BB84, was proposed by Charles Bennett and Gilles Brassard in 1984 and remains the cornerstone of most practical quantum cryptography systems today. The protocol works as follows: the sender, traditionally called Alice, encodes key bits onto individual photons using one of two randomly chosen polarization bases. The receiver, traditionally called Bob, measures each incoming photon using a randomly chosen basis. Alice and Bob then communicate openly — over a classical channel — to compare which bases they each used, discarding the results where their choices did not match. The remaining matching results form a shared secret key.
The critical security property is this: if an eavesdropper — traditionally called Eve — attempts to measure the photons in transit, quantum mechanics dictates that this measurement inevitably disturbs the photons, introducing detectable errors into the key. Alice and Bob can identify this disturbance by comparing a sample of their key bits. If the error rate exceeds a threshold, they know the channel has been compromised and discard the key. If the error rate is acceptably low, they have a provably secure shared key that can be used to encrypt communications.
Real-World QKD Deployments
QKD is no longer confined to laboratory demonstrations. China has built the world’s most extensive quantum communication network, spanning thousands of kilometers and connecting major cities via quantum-secured fiber links and the Micius satellite — the world’s first quantum communication satellite. In Europe, the EuroQCI initiative is building a quantum communication infrastructure across all EU member states. In the United States, national laboratories and financial institutions have been piloting QKD networks in metropolitan areas.
Commercial QKD systems are now available from vendors including ID Quantique, Toshiba, and several Chinese technology companies. While deployment costs remain high and range limitations require quantum repeaters for long distances, the technology has crossed the threshold from research prototype to commercial product.
Quantum Cryptography Applications Across Industries
The highest-value applications of Quantum Cryptography today are concentrated in sectors where the long-term confidentiality of data is critical and the consequences of a security breach are severe:
Government and Defense
National governments and defense agencies worldwide are among the earliest and most serious adopters of quantum cryptographic technologies. For intelligence agencies managing information that must remain classified for decades, the harvest now, decrypt later threat demands immediate action. Several governments have classified quantum-secure communications as critical national security infrastructure and are funding large-scale QKD network deployments.
Financial Services
Banks, payment networks, and financial market infrastructure operators handle transaction data and financial records that must remain confidential and tamper-proof for extended periods. The financial sector is actively piloting both post-quantum cryptography migrations and QKD deployments for the most sensitive inter-bank and central bank communications. The SWIFT global payment network and several central banks have publicly disclosed quantum security upgrade programs.
Healthcare and Life Sciences
Patient health records, genomic data, and clinical trial information represent some of the most sensitive long-lived personal data in existence. A patient’s genomic profile, once stolen, cannot be changed. Healthcare organizations handling this class of data have strong incentives to adopt quantum-resistant and quantum-secure cryptographic protections ahead of the quantum computing threat materializing.
Critical Infrastructure
Power grids, water treatment systems, transportation networks, and telecommunications backbone infrastructure are high-value targets for adversarial cyberattacks — including nation-state actors with access to sophisticated quantum computing capabilities. Securing the control systems and communications of critical infrastructure with quantum cryptographic protections is an active priority for governments and infrastructure operators worldwide.
Quantum Cryptography Challenges Organizations Must Understand
For all its promise, Quantum Cryptography faces genuine practical challenges that any organization evaluating it needs to understand clearly:
- Infrastructure requirements: QKD requires dedicated quantum communication hardware and, for fiber-based systems, specialized quantum-enabled optical networks. This represents a significant capital investment that is not justified for most organizations at current technology maturity levels.
- Distance limitations: Quantum signals degrade over distance due to photon loss and decoherence. Current fiber-based QKD systems typically have practical ranges of 100-200 kilometers without quantum repeaters. Quantum repeaters — devices that can extend QKD range without compromising security — remain an active area of research and are not yet commercially available at scale.
- Integration complexity: Integrating QKD systems with existing classical network infrastructure and key management systems is technically complex. Standards for quantum-classical network integration are still maturing.
- Cost: Commercial QKD systems remain expensive compared to classical cryptographic solutions. For most organizations, the cost-benefit calculation currently favors post-quantum cryptography migration as the immediate priority.
- Side-channel vulnerabilities: While the theoretical security of QKD is information-theoretic, real-world implementations using imperfect hardware have been shown to have side-channel vulnerabilities. Device-independent QKD protocols that are secure even against compromised hardware are an active research area.
What Every Organization Should Do About Quantum Cryptography Now
The question is not whether to take the quantum security threat seriously — it is how to prioritize your response given your organization’s specific risk profile and resources. Here is a practical framework:
Step 1: Conduct a Cryptographic Inventory
Map every system in your organization that uses encryption. Document what algorithms and key lengths are in use, what data those systems protect, and how long that data needs to remain confidential. This inventory is the foundation of your quantum security strategy.
Step 2: Prioritize by Data Longevity and Sensitivity
Systems protecting data that must remain confidential for ten years or more — and particularly data that adversaries have strong incentives to collect now and decrypt later — are your highest priority. Classify your systems accordingly and focus your near-term investment here.
Step 3: Begin Post-Quantum Cryptography Migration
For the vast majority of organizations, the immediate action item is not deploying QKD hardware — it is migrating to NIST-standardized post-quantum cryptographic algorithms. Begin with your highest-priority systems and plan a phased migration across your broader infrastructure. This is a multi-year program for most large organizations and should start now.
Step 4: Adopt a Crypto-Agile Architecture
Crypto-agility means designing your systems so that cryptographic algorithms can be swapped out without major architectural changes. This is the defensive posture that protects you against future cryptographic vulnerabilities — quantum or otherwise. It is a best practice that pays dividends far beyond quantum security.
Step 5: Monitor the QKD Landscape
If your organization operates in a sector where long-term data confidentiality is critical — government, defense, financial services, healthcare — begin tracking the maturity and cost trajectory of commercial QKD solutions. The economics are improving every year, and the infrastructure is expanding. Understanding when the technology becomes appropriate for your specific needs requires staying current with the market.
Final Thoughts: Quantum Cryptography Is Not Optional — It Is Inevitable
Quantum Cryptography represents the frontier of digital security in an era when the mathematical foundations of classical encryption are under existential threat. The technology is advancing rapidly, the threat is already partially active through harvest now, decrypt later strategies, and the window for proactive preparation is open — but it is not unlimited.
Organizations that begin their quantum security journey today — starting with cryptographic inventories, post-quantum migrations, and crypto-agile architectures — will be dramatically better positioned than those that wait for quantum computers to arrive before acting. By that point, the window for orderly, proactive transition will have closed.
The future of digital security is quantum. The organizations that understand Quantum Cryptography, invest in the right protections at the right time, and build the institutional knowledge needed to navigate this transition will be the ones that emerge from the quantum era with their data, their reputations, and their competitive positions intact