Zero Trust Security: The New Gold Standard for Cyber Defense in 2026
The old security model assumed everyone inside your network could be trusted. Zero Trust Security assumes the opposite — and in 2026, that shift is saving organizations from breaches that traditional defenses never could have stopped.
Zero Trust Security is the cybersecurity framework that starts from a single, radical premise: trust no one and verify everything. Not external attackers. Not internal employees. Not devices already inside your network. Nobody gets access to anything without being continuously authenticated, authorized, and validated — every single time, for every single request. In 2026, Zero Trust Security has moved from a cutting-edge concept discussed at security conferences to the dominant enterprise security model adopted by governments, Fortune 500 companies, and fast-growing businesses across every industry.
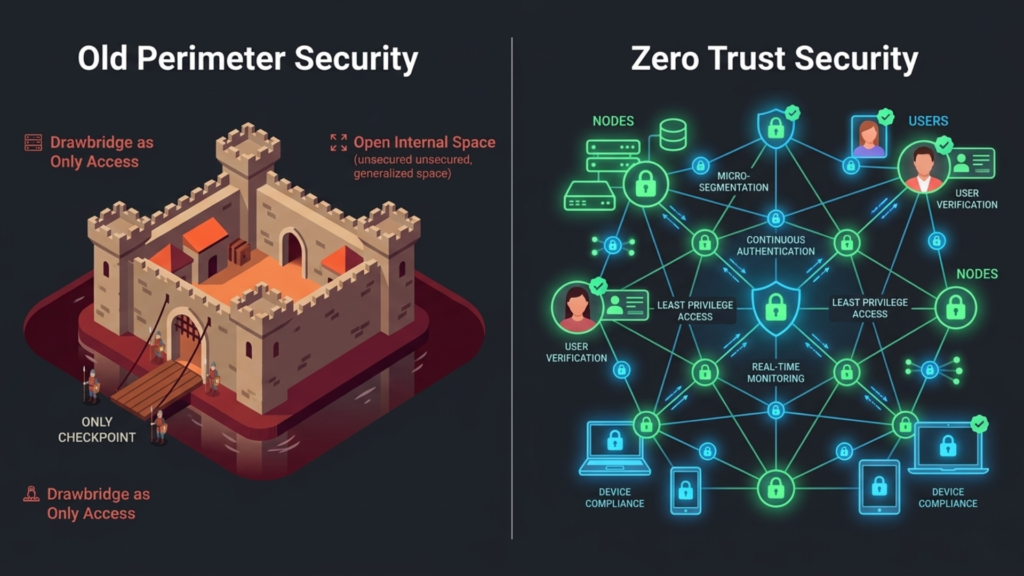
The reason for this shift is not philosophical — it is practical. The traditional security model, often called the castle-and-moat approach, was built for a world that no longer exists. In that world, everything inside your corporate network was trusted and everything outside was suspect. You built a strong perimeter — firewalls, VPNs, access controls at the boundary — and assumed that anything already inside was safe.
That model has been broken for years. Remote work, cloud computing, mobile devices, third-party vendors, and increasingly sophisticated attackers who specialize in getting inside perimeters have made the very concept of a trusted network boundary obsolete. Zero Trust Security is the answer to that broken model — and in this article, we explain exactly what it is, how it works, why it matters so much right now, and how your organization can begin implementing it.
What Is Zero Trust Security? The Core Philosophy Explained
The term Zero Trust was coined by Forrester Research analyst John Kindervag in 2010, but the framework has evolved significantly since then and has become far more urgent and far more actionable in recent years.
At its heart, Zero Trust Security is built on three foundational principles that represent a complete departure from traditional security thinking:
- Never trust, always verify: No user, device, application, or network connection is trusted by default — regardless of whether it is inside or outside the corporate network. Every access request must be authenticated and authorized before it is granted.
- Assume breach: Zero Trust operates on the assumption that a breach has already occurred or will occur. Rather than focusing solely on keeping attackers out, it focuses on limiting the damage an attacker can do once they are in. This means minimizing access rights, segmenting networks, and monitoring everything continuously.
- Least privilege access: Every user, device, and application receives only the minimum level of access needed to perform its specific function — and nothing more. Broad, sweeping access rights are replaced with narrow, specific, time-limited permissions.
Zero Trust Security does not mean you distrust your employees. It means you have built a system where even if an employee’s credentials are stolen, an attacker still cannot move freely through your organization.
This philosophy has profound implications for how organizations design their networks, manage identities, deploy applications, and monitor for threats. It is not a single product you can buy — it is an architecture, a mindset, and an ongoing operational practice.
Why Zero Trust Security Has Become Essential in 2026
Understanding why Zero Trust Security has become the dominant framework in 2026 requires understanding how dramatically the threat landscape and the technology environment have changed:
The Death of the Network Perimeter
Ten years ago, most corporate data lived on servers inside a physical office, accessed by employees sitting at desks connected to a local network. The perimeter was real and defensible. Today, data lives in multiple cloud platforms, employees work from home, coffee shops, and airports, applications run as SaaS services outside any corporate network, and business processes depend on dozens of third-party vendors with their own access to your systems. There is no perimeter anymore. Defending something that does not exist is not a viable security strategy.
The Insider Threat Problem
Traditional security models assumed that people and devices already inside the network could be trusted. But some of the most damaging breaches in recent history have originated from inside — whether through malicious insiders, compromised employee credentials, or trusted vendors whose own systems were breached and used as stepping stones. Zero Trust Security treats every access request with the same scrutiny regardless of its origin, eliminating the blind spot that inside-the-perimeter trust creates.
The Rise of Ransomware and Lateral Movement
Modern ransomware attacks typically do not encrypt a single machine and demand payment. They infiltrate through a low-privilege entry point — a phishing email, a compromised vendor account, a vulnerable internet-facing system — and then move laterally through the network, escalating privileges and spreading to as many systems as possible before triggering the final attack. Zero Trust Security’s principle of micro-segmentation and least privilege access directly addresses lateral movement: even if an attacker gains a foothold, they cannot move freely because access to each additional system requires separate authentication and authorization.
Regulatory and Compliance Pressure
Governments and regulatory bodies worldwide have increasingly incorporated Zero Trust principles into their cybersecurity requirements. The US federal government mandated Zero Trust architecture adoption across all federal agencies through executive order. The EU’s NIS2 Directive, which came into force for a broad range of critical sectors, incorporates Zero Trust principles into its security requirements. For many organizations, Zero Trust is not just best practice — it is a compliance requirement.
The Five Pillars of Zero Trust Security Architecture
Zero Trust Security is not a single technology — it is an architecture built across five interconnected pillars. Understanding these pillars is essential for anyone planning or evaluating a Zero Trust implementation:
- Identity
Identity is the foundation of Zero Trust Security. Every user, service account, and non-human entity that requests access to any resource must have a verified identity. This requires robust identity and access management infrastructure — multi-factor authentication, single sign-on, privileged access management, and continuous behavioral monitoring that can detect when an account’s activity deviates from its normal pattern. In Zero Trust, identity is the new perimeter.
- Devices
Every device requesting access to corporate resources must be verified and assessed before access is granted. Is this device known and registered? Does it meet minimum security requirements — up-to-date operating system, active endpoint protection, disk encryption? Is it showing any signs of compromise? Device health is checked continuously, not just at the moment of initial login. A device that passes a check at 9am but becomes compromised at 11am should have its access revoked automatically.
- Networks
Zero Trust replaces the flat, open corporate network with micro-segmented network architecture. Rather than connecting everything to a single internal network where lateral movement is easy, systems and data are divided into small segments with strict controls on what can communicate with what. Even inside the corporate network, a device in one segment cannot freely reach resources in another segment without explicit authorization. This dramatically limits the blast radius of any breach.
- Applications and Workloads
Applications — whether running on-premises, in the cloud, or as SaaS services — must enforce access controls at the application layer rather than relying on network-level controls. This means applications authenticate users independently, enforce least-privilege access to their own resources, and do not assume that network access equals application access. Every API call, every database query, every microservice interaction is treated as a potential trust boundary. - Data
Ultimately, everything in Zero Trust Security is about protecting data. Data must be classified by sensitivity, and access policies must be enforced based on that classification. Data at rest and in transit must be encrypted. Data access must be logged and monitored for anomalous patterns. The goal is to ensure that even if every other control fails, the data itself remains protected — through encryption, rights management, and data loss prevention systems that prevent unauthorized exfiltration.
Zero Trust Security in Practice: Real-World Implementations
Zero Trust Security is not just a framework on paper — it is being implemented at scale by leading organizations across every sector. Here is what real Zero Trust deployments look like:
Google’s Beyond Corp — The Model That Started It All
Google is widely credited with the first large-scale, real-world Zero Trust implementation. After a sophisticated cyberattack in 2009, Google undertook a complete redesign of its internal security architecture under a program called Beyond Corp. The core insight was to move access controls from the network perimeter to individual devices and users — making the network itself irrelevant to access decisions. An employee could work from any network, anywhere in the world, and access corporate resources with the same level of security as if they were sitting in a Google office. Beyond Corp became the template that the entire industry has since followed.
US Federal Government Zero Trust Mandate
In 2021, the US federal government issued an executive order requiring all federal agencies to develop and implement Zero Trust Security architectures. The Office of Management and Budget subsequently published a detailed federal Zero Trust strategy with specific, measurable targets covering identity, devices, networks, applications, and data. By 2026, federal agencies are well into the implementation journey, and the lessons learned from the largest Zero Trust deployment in history are informing best practices across the private sector.
Financial Services Sector Adoption
Major banks and financial institutions have been among the most aggressive private sector adopters of Zero Trust Security. The combination of regulatory pressure, the high value of financial data as an attack target, and the complexity of modern financial infrastructure — spanning cloud platforms, legacy systems, third-party fintech integrations, and global networks — makes Zero Trust not just attractive but necessary. Leading banks now enforce continuous verification for every internal system access, regardless of whether the request originates from inside or outside the corporate network.
Zero Trust Security: Common Mistakes to Avoid
Zero Trust implementations fail more often than they should — typically not because the framework is flawed but because of predictable implementation mistakes. Here are the most common pitfalls:
- Treating Zero Trust as a product purchase: No single vendor product delivers Zero Trust. Organizations that buy a tool marketed as a Zero Trust solution and consider the job done are dangerously mistaken. Zero Trust is an architecture that requires coordinated changes across identity management, network design, application security, and data protection — implemented over time with clear strategy and governance.
- Trying to do everything at once: Zero Trust transformation is a multi-year journey, not a project with a completion date. Organizations that attempt to implement all five pillars simultaneously typically stall, run over budget, and create operational disruption. A phased approach — starting with identity and high-value assets — produces far better outcomes.
- Neglecting user experience: Security controls that are too cumbersome will be circumvented. Zero Trust implementations must balance security rigor with usability. If employees find the friction of constant verification too disruptive, they will find workarounds that undermine the entire model. Good Zero Trust design is largely invisible to users who are doing their normal jobs.
- Skipping the discovery phase: Many organizations underestimate how poorly they understand their own data flows, application dependencies, and access patterns before beginning Zero Trust implementation. A thorough discovery and mapping exercise — understanding what data exists, where it lives, who accesses it, and how it moves — is essential groundwork that cannot be skipped.
- Ignoring non-human identities: Modern enterprise environments have as many or more non-human identities — service accounts, API keys, application credentials, automated processes — as human ones. Zero Trust must cover the full identity landscape, not just human users. Non-human identities are a frequently exploited attack vector in organizations that focus exclusively on human user security.
How to Begin Your Zero Trust Security Journey
Zero Trust transformation does not have to be overwhelming. Here is a practical starting framework that works for organizations of any size:
Step 1: Know Your Crown Jewels
Start by identifying your most critical and sensitive data and systems — the assets that, if compromised, would cause the most serious harm to your organization. These are your crown jewels, and they are where your Zero Trust controls should be strongest and where your implementation should begin.
Step 2: Map All Access Paths
Document who accesses what, from where, using which devices and applications. This map — covering both human and non-human identities — is the foundation of your Zero Trust policy design. You cannot enforce least privilege access if you do not know what access currently exists.
Step 3: Strengthen Identity and Multi-Factor Authentication
Identity is the first and most impactful pillar to address. Deploy multi-factor authentication universally — not just for privileged accounts but for every user and every application. Implement single sign-on to consolidate identity management. Deploy behavioral analytics that can detect anomalous account activity. These steps deliver immediate, significant security improvements and lay the foundation for the rest of your Zero Trust architecture.
Step 4: Implement Micro-Segmentation
Begin segmenting your network, starting with the segments that contain your most sensitive data and systems. Define explicit rules for what traffic is permitted between segments and deny everything else by default. This limits lateral movement and is one of the most effective controls against ransomware and advanced persistent threats.
Step 5: Invest in Continuous Monitoring
Zero Trust is not a set-and-forget architecture. It requires continuous monitoring of user behavior, device health, network traffic, and application activity to detect anomalies and respond to threats in real time. Invest in security information and event management, user behavior analytics, and automated response capabilities that can act on detections faster than human analysts alone.
Final Thoughts: Zero Trust Security Is Not Optional Anymore
Zero Trust Security has earned its place as the gold standard of modern cybersecurity not because it is trendy but because it is correct. The assumptions underlying traditional perimeter-based security have been invalidated by cloud computing, remote work, supply chain complexity, and the relentless sophistication of modern attackers. Zero Trust replaces those broken assumptions with an architecture built for the real threat environment organizations face today.
The organizations that have committed to Zero Trust Security are not just better protected against today’s attacks — they are building the security foundations that will scale with them as their technology environments grow more complex, as AI-powered attacks become more sophisticated, and as the regulatory environment for cybersecurity continues to tighten.
Starting a Zero Trust journey is not easy, and completing it takes years of disciplined effort. But the organizations that begin now — with a clear strategy, a phased approach, and strong leadership commitment — will be the ones that emerge from the increasingly dangerous cyber landscape of the late 2020s with their data, their reputations, and their businesses intact. Read More Blogs